If I set a user interface password will my backup encryption passphrases be stored in a secure way on my local storage?
I believe it’s stored ‘salted’ in the SQLite database. So a plaintext search won’t find it, but it can be reversed using advanced tools. Use the OS to ensure other computer users don’t have access to your profile data and you should be fine.
Welcome to the forum @jby96032
is not related to
seems to be true for the user interface password. Commonly a salted hash tests user password entry.
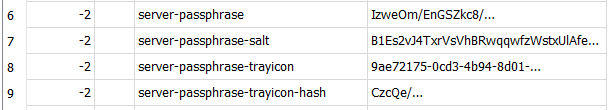
Life is different when the passphrase (not just hash) must be used, e.g. for encryption and decryption.
There’s a similar need to obtain actual credentials when talking to a remote service for authentication.
On Windows, the entire settings database is encrypted with (weak) encryption and a default fixed key.
This is enough to stop simple scanners. On Linux, I think the SQLite library usually lacks this ability…
Which tool can open encrypted DB has some info, and shows that it’s a bit hard to read Windows DB.
Mine is geared towards reading (because I sometimes debug), so I option to –unencrypted-database.
One person used a VeraCrypt volume. Ultimately an attacker on-system can probably read password. Because Duplicati has to use it, an attacker with a debugger can grab it at the point of its internal use.
It’s kind of a matter of how easy or hard we make it on attackers. There is an open Issue in the queue.
Meanwhile Windows helps, and OS access control helps, especially if Duplicati is set up as a Service.