We’re now trying to determine if that’s a Duplicati problem or if your files are truly corrupted or encrypted by ransomware (what are the file dates – normally you would have a range?). Bypassing Duplicati to do direct decryption answers the question.
I have only cloud backup left which I can’t restore because of error messages.
I have more than 200gb data. I need to recover as soon as possible.
Yes if you help me I can give you my TeamViewer ID.
Can you please email me? it’s nikunjkatharotiya1612@gmail.com
I had first backup files from Feb and last was April 27.
Even I can restore from Feb it’s fine to
Is this data corporate or personal?
If it is corporate, are you authorized to allow access to it?
You’re talking about actual current OneDrive file dates I hope. If so, good news, but we still need to figure out the decryption problem by either your showing the error, or trying AES Crypt to see if that can decrypt files…
It’s small business data. Yes, I’m authorized to access data. Can we talk on email and I can provide my team viewer id?
I’m leaving a client site now, I’ll email you after I get home
Yes, It’s one drive backup dates. How can we check data is not corrupted? I had to make new account because I don’t able to reply from that account for next 18 hours.
Exactly like I’ve been saying. Decrypt with something. That’s the main question at the moment. If it decrypts, testing with a ZIP program is a bonus, however the encrypted form has enough self-checking that corruption should be revealed at that level. If you can get a full set of unencrypted ZIP files, there’s a good chance of the recovery getting something (hope all) back even if it needs help (hopefully it won’t). Decryption is essential…
EDIT:
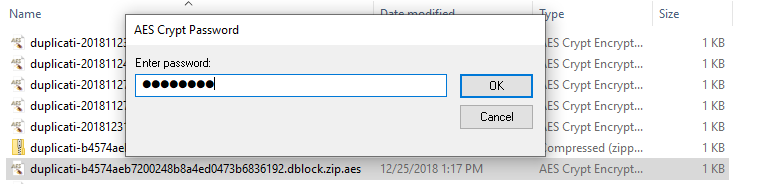
AES Crypt User Guide page 7 shows a decrypt. Short answer is right click, choose AES Decrypt, type password. Here’s what it looks like on the example file that I used for the SharpAESCrypt output earlier:
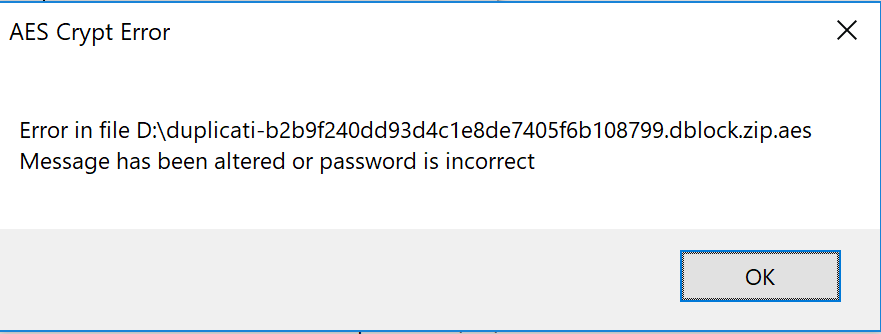
I try this one it working fine with my other computer data which is not affected by the virus. When I try to do with affected data it giving me error. I have shared the error message.
Is there any way we can recover corrupted data?
Checking your other computer was a good idea. For the affected one, I wonder if the ransomware got it somehow, while maintaining original date? If you have the affected computer drive, you could see if that pattern happened there, meaning file date is reasonable but file content is encrypted by the ransomware.
Restore your OneDrive shows that if you have Office 365 you might still be able to undo remote damage.
Confirming the file is very messed up is probably best done with a hex viewer such as Frhed. If you drag some .zip.aes file onto its window, a properly built AES file should have some readable text, for example
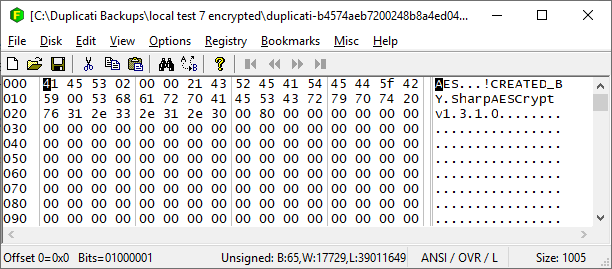
It’d be interesting to look at one of the ransomware-bitten files to see if it leaves any signature info inside. Without that, we’re still not sure if ransomware hit your backup or if somehow Duplicati put up a bad file, however once again having a second computer can be useful for comparison, and apparently that’s OK.
EDIT:
made me hope the computer itself had no file access to OneDrive. If it had access, ransomware did too. You could look on your other computer to see if Duplicati’s backup files can be seen in your File Explorer.
I’ve sent you an email from nathan@mccarty.io
Was the ransomware quite thorough, e.g. did it get all the users? If so, I’d guess it got Duplicati’s databases.
If you installed it as a Windows service (needs the CLI, not just GUI installer), then hope might be a bit more. Being able to look in that would have given some clues about the expected state (e.g. length) of remote files. Databases can be recreated from the backup files, but not if the backup files have been ransomware-taken.
I’m assuming the Duplicati that’s giving basically the same error as AES Crypt is on the unaffected machine, doing a “direct restore” or something similar. You wouldn’t normally have a local database there ready-to-run.
Hello @Nathan_McCarty,
Thanks for offering to go take a look on the system. To throw some code detail at you just in case you’re able to use it, the AES Crypt file format that’s expected is documented here, including readable headers I showed.
The “Invalid password or corrupted data” is probably raised here, after the extension blocks are read through, however if the readable headers are consistently not visible in a hex viewer, I’d think that’s a really bad sign…
Good luck, and I’ll be around for at least a few more hours to try to help you or anybody with whatever arises.
Hello @ts678, We recover the data with the help of @Nathan_McCarty.
We are greatly appreciated. Nathan did a really good job and hard work.
Thank you @ts678 for your help and time.
Thank you, everyone, for the help and the hard work.
Glad someone was able to help. I’d be curious to hear further feedback from @Nathan_McCarty regarding what issues there were and what resolution steps worked, just so the rest of us have a clearer idea for starting points in future troubleshooting efforts.
99% of the effort was pulling down a good copy of the backup files and getting them decrypted. For its part, duplicati wasn’t actually the issue. Though it did encounter the “hit a wall at 70% database rebuild completion” error, the built in recovery tool worked fine.
Nice job going above and beyond to help!